[ad_1]
Microsoft on Friday shared guidance to help customers discover indicators of compromise (IoCs) associated with a recently patched Outlook vulnerability.
Tracked as CVE-2023-23397 (CVSS score: 9.8), the critical flaw relates to a case of privilege escalation that could be exploited to steal NT Lan Manager (NTLM) hashes and stage a relay attack without requiring any user interaction.
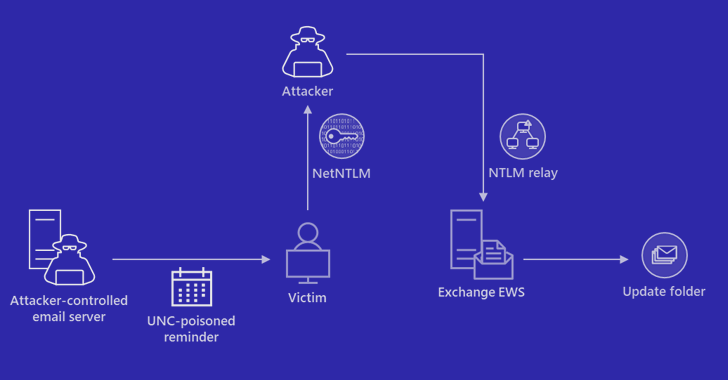
“External attackers could send specially crafted emails that will cause a connection from the victim to an untrusted location of attackers’ control,” the company noted in an advisory released this month.
“This will leak the Net-NTLMv2 hash of the victim to the untrusted network which an attacker can then relay to another service and authenticate as the victim.”
The vulnerability was resolved by Microsoft as part of its Patch Tuesday updates for March 2023, but not before Russia-based threat actors weaponized the flaw in attacks targeting government, transportation, energy, and military sectors in Europe.
Microsoft’s incident response team said it found evidence of potential exploitation of the shortcoming as early as April 2022.
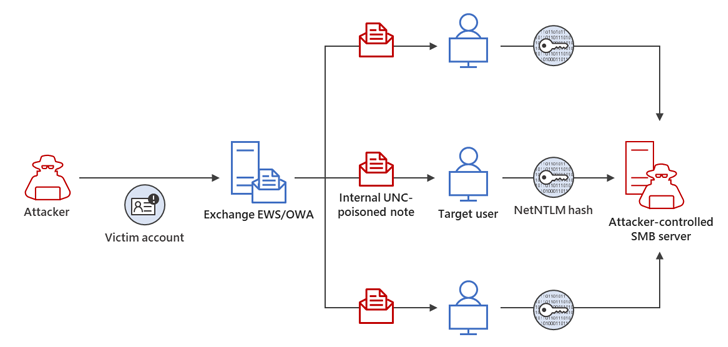
In one attack chain described by the tech giant, a successful Net-NTLMv2 Relay attack enabled the threat actor to gain unauthorized access to an Exchange Server and modify mailbox folder permissions for persistent access.
The compromised email account was then used to extend the adversary’s access within the compromised environment by sending additional malicious messages to target other members of the same organization.
“While leveraging NTLMv2 hashes to gain unauthorized access to resources is not a new technique, the exploitation of CVE-2023-23397 is novel and stealthy,” Microsoft said.
“Organizations should review SMBClient event logging, Process Creation events, and other available network telemetry to identify potential exploitation via CVE-2023-23397.”
Discover the Hidden Dangers of Third-Party SaaS Apps
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions being granted and how to minimize risk.
The disclosure comes as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) released a new open source incident response tool that helps detect signs of malicious activity in Microsoft cloud environments.
Dubbed Untitled Goose Tool, the Python-based utility offers “novel authentication and data gathering methods” to analyze Microsoft Azure, Azure Active Directory, and Microsoft 365 environments, the agency said.
Earlier this year, Microsoft also urged customers to keep their on-premises Exchange servers updated as well as take steps to bolster their networks to mitigate potential threats.
[ad_2]
Source link