[ad_1]
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday disclosed details of a “novel persistent backdoor” called SUBMARINE deployed by threat actors in connection with the hack on Barracuda Email Security Gateway (ESG) appliances.
“SUBMARINE comprises multiple artifacts — including a SQL trigger, shell scripts, and a loaded library for a Linux daemon — that together enable execution with root privileges, persistence, command and control, and cleanup,” the agency said.
The findings come from an analysis of malware samples obtained from an unnamed organization that had been compromised by threat actors exploiting a critical flaw in ESG devices, CVE-2023-2868 (CVSS score: 9.8), which allows for remote command injection.
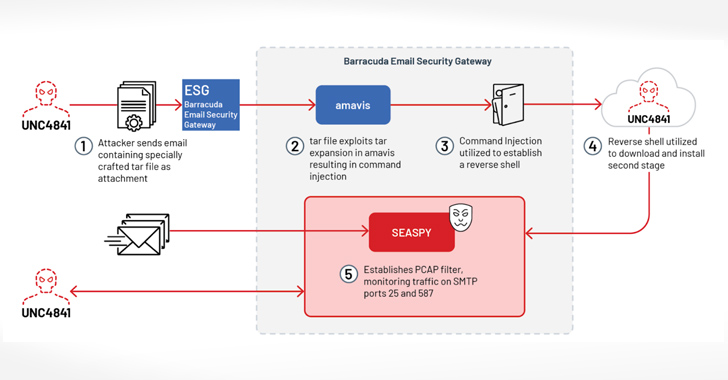
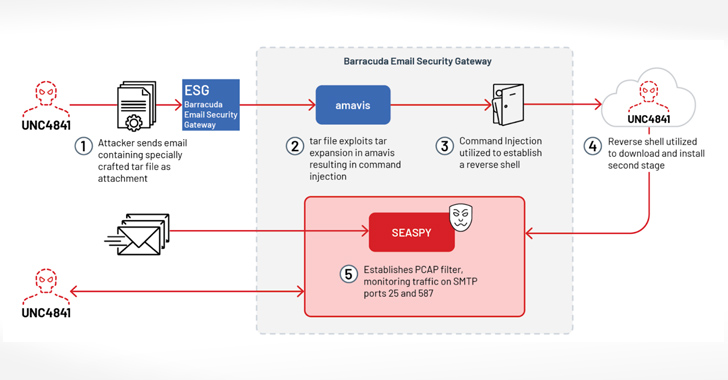
Evidence gathered so far shows that the attackers behind the activity, a suspected China nexus-actor tracked by Mandiant as UNC4841, leveraged the flaw as a zero-day in October 2022 to gain initial access to victim environments and implanted backdoors to establish and maintain persistence.
To that end, the infection chain involved sending phishing emails with booby-trapped TAR file attachments to trigger exploitation, leading to the deployment of a reverse shell payload to establish communication with the threat actor’s command-and-control (C2) server, from where a passive backdoor known as SEASPY is downloaded for executing arbitrary commands on the device.
SUBMARINE, also codenamed DEPTHCHARGE by the Google-owned threat intelligence firm, is the latest malware family to be discovered in connection with the operation. Executed with root privileges, it resides in a Structured Query Language (SQL) database on the ESG appliance.
Shield Against Insider Threats: Master SaaS Security Posture Management
Worried about insider threats? We’ve got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
It’s believed to have been “deployed in response to remediation efforts,” echoing Mandiant’s characterization of the adversary as an aggressive actor capable of quickly altering their malware and employing additional persistence mechanisms in an attempt to maintain their access.
The agency further said it “analyzed artifacts related to SUBMARINE that contained the contents of the compromised SQL database,” and that it “poses a severe threat for lateral movement.”
[ad_2]
Source link