[ad_1]
Cybersecurity researchers have disclosed a new sophisticated Android malware called FjordPhantom that has been observed targeting users in Southeast Asian countries like Indonesia, Thailand, and Vietnam since early September 2023.
“Spreading primarily through messaging services, it combines app-based malware with social engineering to defraud banking customers,” Oslo-based mobile app security firm Promon said in an analysis published Thursday.
Propagated mainly via email, SMS, and messaging apps, attack chains trick recipients into downloading a purported banking app that comes fitted with legitimate features but also incorporates rogue components.
Victims are then subjected to a social engineering technique akin to telephone-oriented attack delivery (TOAD), which involves calling a bogus call center to receive step-by-step instructions for running the app.
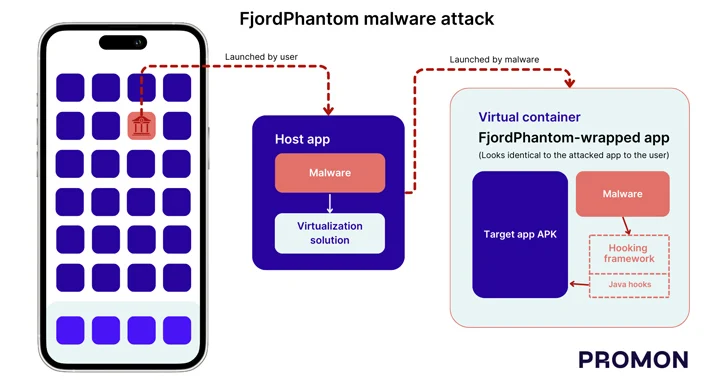
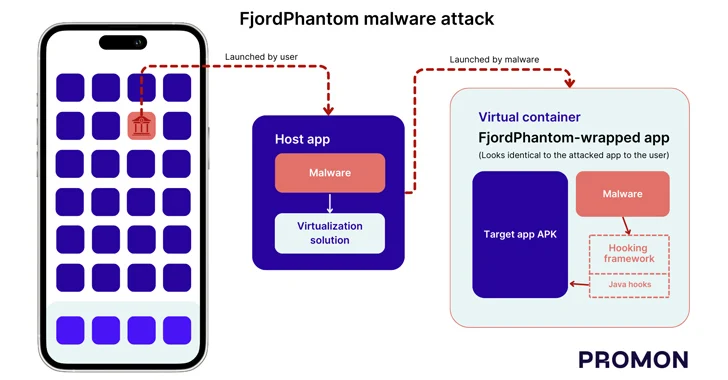
A key characteristic of the malware that sets it apart from other banking trojans of its kind is the use of virtualization to run malicious code in a container and fly under the radar.
The sneaky method, Promon said, breaks Android’s sandbox protections as it allows different apps to be run on the same sandbox, enabling the malware to access sensitive data without requiring root access.
“Virtualization solutions like the one used by the malware can also be used to inject code into an application because the virtualization solution first loads its own code (and everything else found in its app) into a new process and then loads the code of the hosted application,” security researcher Benjamin Adolphi said.
In the case of FjordPhantom, the host app downloaded includes a malicious module and the virtualization element that’s then used to install and launch the embedded app of the targeted bank in a virtual container.
In other words, the bogus app is engineered to load the bank’s legitimate app in a virtual container while also employing a hooking framework within the environment to alter the behavior of key APIs to grab sensitive information from the application’s screen programmatically and close dialog boxes used to warn malicious activity on users’ devices.
“FjordPhantom itself is written in a modular way to attack different banking apps,” Adolphi said. “Depending on which banking app is embedded into the malware, it will perform various attacks on these apps.”
[ad_2]
Source link