[ad_1]
Threat actors affiliated with the Democratic People’s Republic of Korea (also known as North Korea) have plundered at least $600 million in cryptocurrency in 2023.
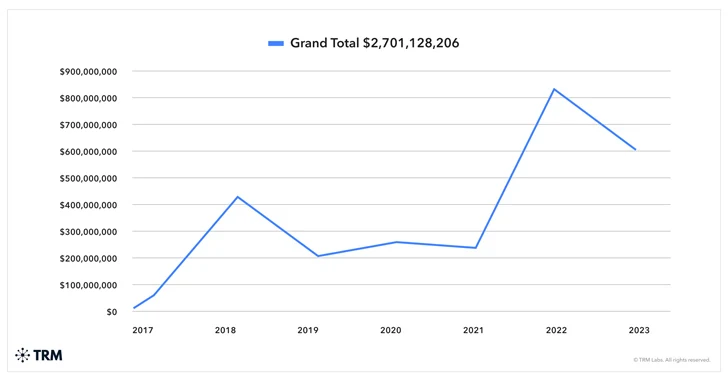
The DPRK “was responsible for almost a third of all funds stolen in crypto attacks last year, despite a 30% reduction from the USD 850 million haul in 2022,” blockchain analytics firm TRM Labs said last week.
“Hacks perpetrated by the DPRK were on average ten times as damaging as those not linked to North Korea.”
There are indications that additional breaches targeting the crypto sector towards the end of 2023 could push this figure higher to around $700 million.
The targeting of cryptocurrency companies is not new for North Korean state-sponsored actors, who have stolen about $3 billion since 2017.
These financially motivated attacks are seen as a crucial revenue-generation mechanism for the sanctions-hit nation, funding its weapons of mass destruction (WMD) and ballistic missile programs.
The intrusions leverage social engineering to lure targets and typically aim to compromise private keys and seed phrases – which are used to safeguard digital wallets – and then use them to gain unauthorized access to the victims’ assets and transfer them to wallets under the threat actor’s control.
“They are then swapped mostly for USDT or Tron and converted to hard currency using high-volume OTC brokers,” TRM Labs said.
The company further noted that DPRK hackers continued to explore other money laundering tools after the U.S. Treasury Department sanctioned a crypto mixer service known as Sinbad for processing a chunk of their proceeds, indicating constant evolution despite law enforcement pressure.
“With nearly USD 1.5 billion stolen in the past two years alone, North Korea’s hacking prowess demands continuous vigilance and innovation from business and governments,” TRM Labs said.
[ad_2]
Source link