[ad_1]
As many as 200,000 WordPress websites are at risk of ongoing attacks exploiting a critical unpatched security vulnerability in the Ultimate Member plugin.
The flaw, tracked as CVE-2023-3460 (CVSS score: 9.8), impacts all versions of the Ultimate Member plugin, including the latest version (2.6.6) that was released on June 29, 2023.
Ultimate Member is a popular plugin that facilitates the creation of user-profiles and communities on WordPress sites. It also provides account management features.
“This is a very serious issue: unauthenticated attackers may exploit this vulnerability to create new user accounts with administrative privileges, giving them the power to take complete control of affected sites,” WordPress security firm WPScan said in an alert.
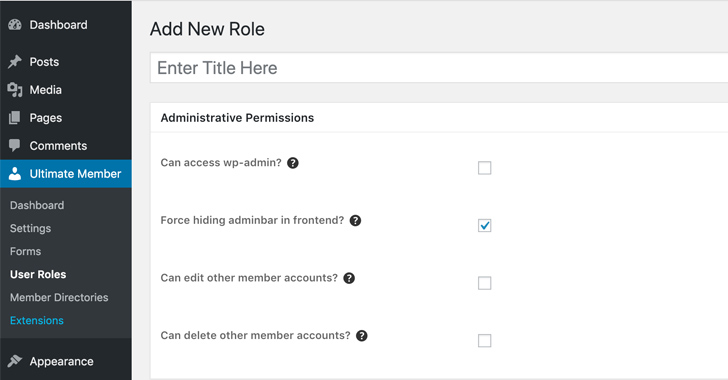
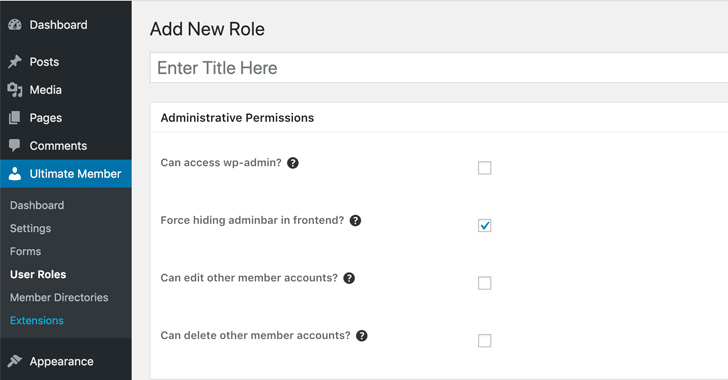
Although details about the flaw have been withheld due to active abuse, it stems from an inadequate blocklist logic put in place to alter the wp_capabilities user meta value of a new user to that of an administrator and gain full access to the site.
“While the plugin has a preset defined list of banned keys, that a user should not be able to update, there are trivial ways to bypass filters put in place such as utilizing various cases, slashes, and character encoding in a supplied meta key value in vulnerable versions of the plugin,” Wordfence researcher Chloe Chamberland said.
The issue came to light after reports emerged of rogue administrator accounts being added to the affected sites, prompting the plugin maintainers to issue partial fixes in versions 2.6.4, 2.6.5, and 2.6.6. A new update is expected to be released in the coming days.
“A privilege escalation vulnerability used through UM Forms,” Ultimate Member said in its release notes. “Known in the wild that vulnerability allowed strangers to create administrator-level WordPress users.”
WPScan, however, pointed out that the patches are incomplete and that it found numerous methods to circumvent them, meaning the issue is still actively exploitable.
In the observed attacks, the flaw is being used to register new accounts under the names apadmins, se_brutal, segs_brutal, wpadmins, wpengine_backup, and wpenginer to upload malicious plugins and themes through the site’s administration panel.
Users of Ultimate Member are advised to disable the plugin until a proper patch that completely plugs the security hole is made available. It’s also recommended to audit all administrator-level users on the websites to determine if any unauthorized accounts have been added.
[ad_2]
Source link