[ad_1]
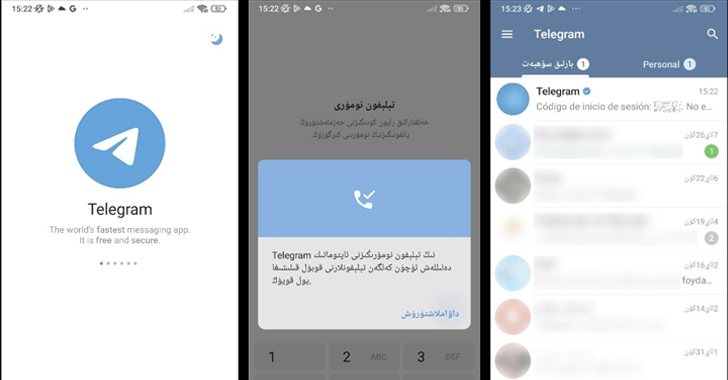
Spyware masquerading as modified versions of Telegram have been spotted in the Google Play Store that’s designed to harvest sensitive information from compromised Android devices.
According to Kaspersky security researcher Igor Golovin, the apps come with nefarious features to capture and exfiltrate names, user IDs, contacts, phone numbers, and chat messages to an actor-controlled server.
The activity has been codenamed Evil Telegram by the Russian cybersecurity company.
The apps have been collectively downloaded millions of times before they were taken down by Google. Their details are as follows –
- 電報,紙飛機-TG繁體中文版 or 電報,小飛機-TG繁體中文版 (org.telegram.messenger.wab) – 10 million+ downloads
- TG繁體中文版-電報,紙飛機 (org.telegram.messenger.wab) – 50,000+ downloads
- 电报,纸飞机-TG简体中文版 (org.telegram.messenger.wob) – 50,000+ downloads
- 电报,纸飞机-TG简体中文版 (org.tgcn.messenger.wob) – 10,000+ downloads
- ئۇيغۇر تىلى TG – تېلېگرامما (org.telegram.messenger.wcb) – 100+ downloads
The last app on the list translates to “Telegram – TG Uyghur,” indicating a clear attempt to target the Uyghur community.
It’s worth noting that the package name associated with the Play Store version of Telegram is “org.telegram.messenger,” whereas the package name for the APK file directly downloaded from Telegram’s website is “org.telegram.messenger.web.”
The use of “wab,” “wcb,” and “wob” for the malicious package names, therefore, highlights the threat actor’s reliance on typosquatting techniques in order to pass off as the legitimate Telegram app and slip under the radar.
Way Too Vulnerable: Uncovering the State of the Identity Attack Surface
Achieved MFA? PAM? Service account protection? Find out how well-equipped your organization truly is against identity threats
“At first glance, these apps appear to be full-fledged Telegram clones with a localized interface,” the company said. “Everything looks and works almost the same as the real thing. [But] there is a small difference that escaped the attention of the Google Play moderators: the infected versions house an additional module:”
The disclosure comes days after ESET revealed a BadBazaar malware campaign targeting the official app marketplace that leveraged a rogue version of Telegram to amass chat backups.
Similar copycat Telegram and WhatsApp apps were uncovered by the Slovak cybersecurity company previously in March 2023 that came fitted with clipper functionality to intercept and modify wallet addresses in chat messages and redirect cryptocurrency transfers to attacker-owned wallets.
[ad_2]
Source link