[ad_1]
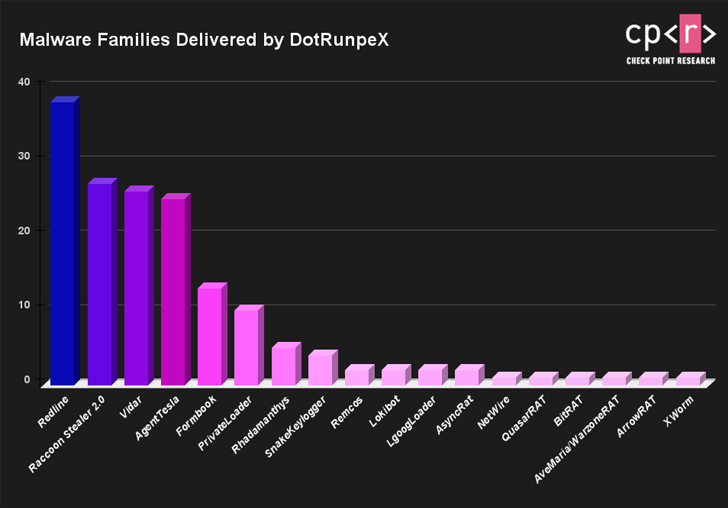
A new piece of malware dubbed dotRunpeX is being used to distribute numerous known malware families such as Agent Tesla, Ave Maria, BitRAT, FormBook, LokiBot, NetWire, Raccoon Stealer, RedLine Stealer, Remcos, Rhadamanthys, and Vidar.
“DotRunpeX is a new injector written in .NET using the Process Hollowing technique and used to infect systems with a variety of known malware families,” Check Point said in a report published last week.
Said to be in active development, dotRunpeX arrives as a second-stage malware in the infection chain, often deployed via a downloader (aka loader) that’s transmitted through phishing emails as malicious attachments.
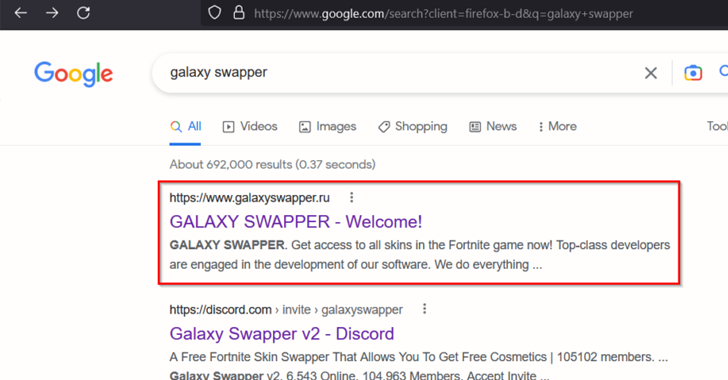
Alternatively, it’s known to leverage malicious Google Ads on search result pages to direct unsuspecting users searching for popular software such as AnyDesk and LastPass to copycat sites hosting trojanized installers.
The latest DotRunpeX artifacts, first spotted in October 2022, add an extra obfuscation layer by using the KoiVM virtualizing protector.
It’s worth pointing out that the findings dovetail with a malvertising campaign documented by SentinelOne last month in which the loader and the injector components were collectively referred to as MalVirt.
Check Point’s analysis has further revealed that “each dotRunpeX sample has an embedded payload of a certain malware family to be injected,” with the injector specifying a list of anti-malware processes to be terminated.
Discover the Hidden Dangers of Third-Party SaaS Apps
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions being granted and how to minimize risk.
This, in turn, is made possible by abusing a vulnerable process explorer driver (procexp.sys) that’s incorporated into dotRunpeX so as to obtain kernel mode execution.
There are signs that dotRunpeX could be affiliated to Russian-speaking actors based on the language references in the code. The most frequently delivered malware families delivered by the emerging threat include RedLine, Raccoon, Vidar, Agent Tesla, and FormBook.
[ad_2]
Source link