[ad_1]
An analysis of the Linux variant of a new ransomware strain called BlackSuit has covered significant similarities with another ransomware family called Royal.
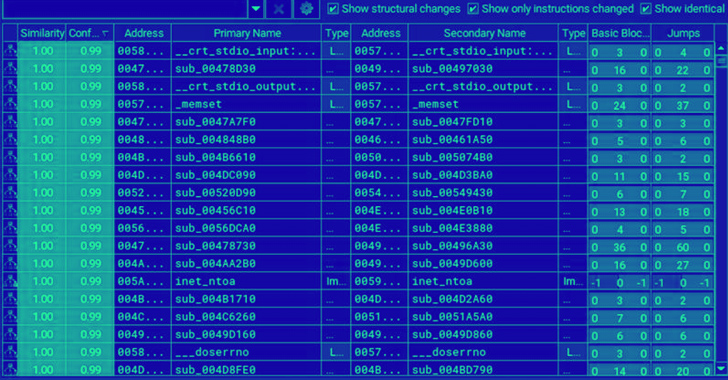
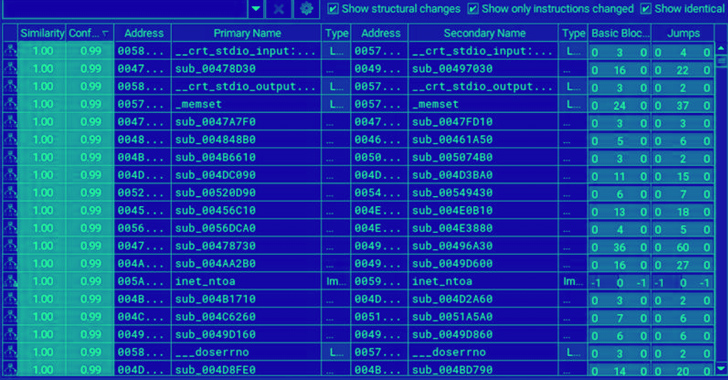
Trend Micro, which examined an x64 VMware ESXi version targeting Linux machines, said it identified an “extremely high degree of similarity” between Royal and BlackSuit.
“In fact, they’re nearly identical, with 98% similarities in functions, 99.5% similarities in blocks, and 98.9% similarities in jumps based on BinDiff, a comparison tool for binary files,” Trend Micro researchers noted.
A comparison of the Windows artifacts has identified 93.2% similarity in functions, 99.3% in basic blocks, and 98.4% in jumps based on BinDiff.
BlackSuit first came to light in early May 2023 when Palo Alto Networks Unit 42 drew attention to its ability to target both Windows and Linux hosts.
In line with other ransomware groups, it runs a double extortion scheme that steals and encrypts sensitive data in a compromised network in return for monetary compensation. Data associated with a single victim has been listed on its dark web leak site.
The latest findings from Trend Micro show that, both BlackSuit and Royal use OpenSSL’s AES for encryption and utilize similar intermittent encryption techniques to speed up the encryption process.
The overlaps aside, BlackSuit incorporates additional command-line arguments and avoids a different list of files with specific extensions during enumeration and encryption.
“The emergence of BlackSuit ransomware (with its similarities to Royal) indicates that it is either a new variant developed by the same authors, a copycat using similar code, or an affiliate of the Royal ransomware gang that has implemented modifications to the original family,” Trend Micro said.
Given that Royal is an offshoot of the erstwhile Conti team, it’s also possible that “BlackSuit emerged from a splinter group within the original Royal ransomware gang,” the cybersecurity company theorized.
The development once again underscores the constant state of flux in the ransomware ecosystem, even as new threat actors emerge to tweak existing tools and generate illicit profits.
🔐 Mastering API Security: Understanding Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join our insightful webinar!
This includes a new ransomware-as-a-service (RaaS) initiative codenamed NoEscape that Cyble said allows its operators and affiliates to take advantage of triple extortion methods to maximize the impact of a successful attack.
Triple extortion refers to a three-pronged approach wherein data exfiltration and encryption is coupled with distributed denial-of-service (DDoS) attacks against the targets in an attempt to disrupt their business and coerce them into paying the ransom.
The DDoS service, per Cyble, is available for an added $500,000 fee, with the operators imposing conditions that forbid affiliates from striking entities located in the Commonwealth of Independent States (CIS) countries.
[ad_2]
Source link