[ad_1]
An unidentified threat actor compromised an application used by multiple entities in Pakistan to deliver ShadowPad, a successor to the PlugX backdoor that’s commonly associated with Chinese hacking crews.
Targets included a Pakistan government entity, a public sector bank, and a telecommunications provider, according to Trend Micro. The infections took place between mid-February 2022 and September 2022.
The cybersecurity company said the incident could be the result of a supply-chain attack, in which a legitimate piece of software used by targets of interest is trojanized to deploy malware capable of gathering sensitive information from compromised systems.
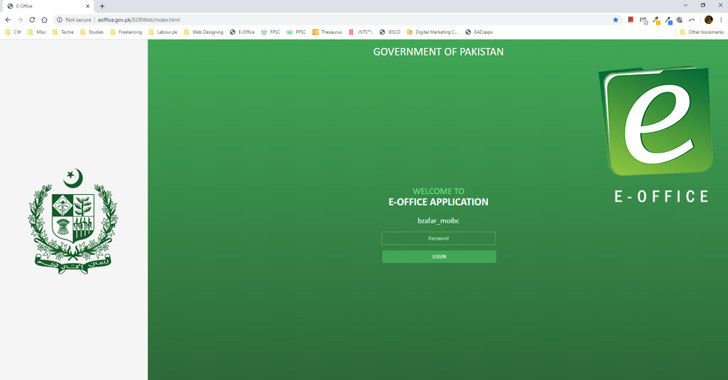
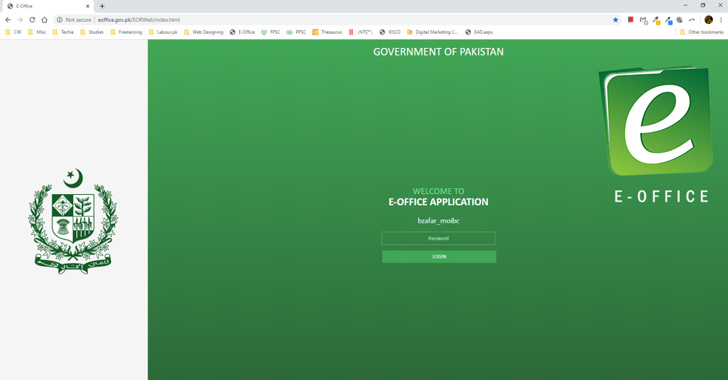
The attack chain takes the form of a malicious installer for E-Office, an application developed by the National Information Technology Board (NITB) of Pakistan to help government departments go paperless.
It’s currently not clear how the backdoored E-Office installer was delivered to the targets. That said, there’s no evidence to date that the build environment of the Pakistani government agency in question has been compromised.
This raises the possibility that the threat actor obtained the legitimate installer and tampered it to include malware, and then subsequently lured victims into running the trojanized version via social engineering attacks.
“Three files were added to the legitimate MSI installer: Telerik.Windows.Data.Validation.dll, mscoree.dll, and mscoree.dll.dat,” Trend Micro researcher Daniel Lunghi said in an updated analysis published today.
Telerik.Windows.Data.Validation.dll is a valid applaunch.exe file signed by Microsoft, which is vulnerable to DLL side-loading and is used to sideload mscoree.dll that, in turn, loads mscoree.dll.dat, the ShadowPad payload.
Trend Micro said the obfuscation techniques used to conceal DLL and the decrypted final-stage malware are an evolution of an approach previously exposed by Positive Technologies in January 2021 in connection with a Chinese cyber espionage campaign undertaken by the Winnti group (aka APT41).
Shield Against Insider Threats: Master SaaS Security Posture Management
Worried about insider threats? We’ve got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
Besides ShadowPad, post-exploitation activities have entailed the use of Mimikatz to dump passwords and credentials from memory.
Attribution to a known threat actor has been hampered by a lack of evidence, although the cybersecurity company said it discovered malware samples such as Deed RAT, which has been attributed to the Space Pirates (or Webworm) threat actor.
“This whole campaign was the result of a very capable threat actor that managed to retrieve and modify the installer of a governmental application to compromise at least three sensitive targets,” Lunghi said.
“The fact that the threat actor has access to a recent version of ShadowPad potentially links it to the nexus of Chinese threat actors, although we cannot point to a particular group with confidence.”
[ad_2]
Source link