[ad_1]
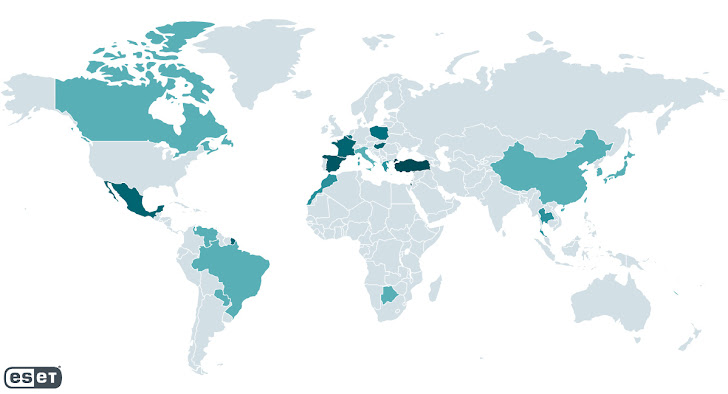
A malicious toolset dubbed Spacecolon is being deployed as part of an ongoing campaign to spread variants of the Scarab ransomware across victim organizations globally.
“It probably finds its way into victim organizations by its operators compromising vulnerable web servers or via brute forcing RDP credentials,” ESET security researcher Jakub Souček said in a detailed technical write-up published Tuesday.
The Slovak cybersecurity firm, which dubbed the threat actor CosmicBeetle, said the origins of the Spacecolon date back to May 2020. The highest concentration of victims has been detected in France, Mexico, Poland, Slovakia, Spain, and Turkey.
While the exact provenance of the adversary is unclear, several Spacecolon variants are said to contain Turkish strings, likely pointing to the involvement of a Turkish-speaking developer. There is no evidence currently linking it to any other known threat actor group.

Some of the targets include a hospital and a tourist resort in Thailand, an insurance company in Israel, a local governmental institution in Poland, an entertainment provider in Brazil, an environmental company in Turkey, and a school in Mexico.
“CosmicBeetle does not choose its targets; rather, it finds servers with critical security updates missing and exploits that to its advantage,” Souček pointed out.
It’s worth noting that Spacecolon was first documented by Polish company Zaufana Trzecia Strona in early February 2023, likely prompting the adversary to tweak its arsenal in response to public disclosures.
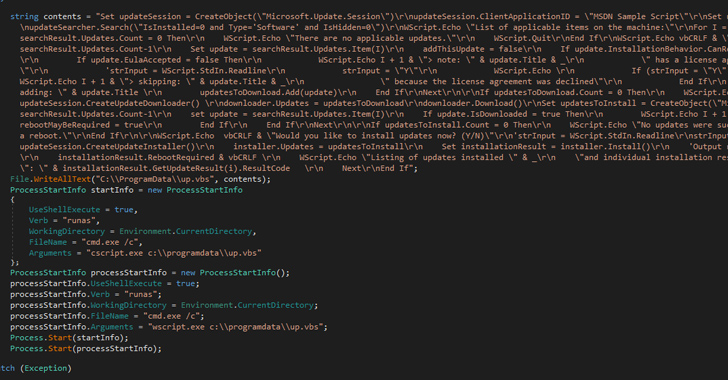
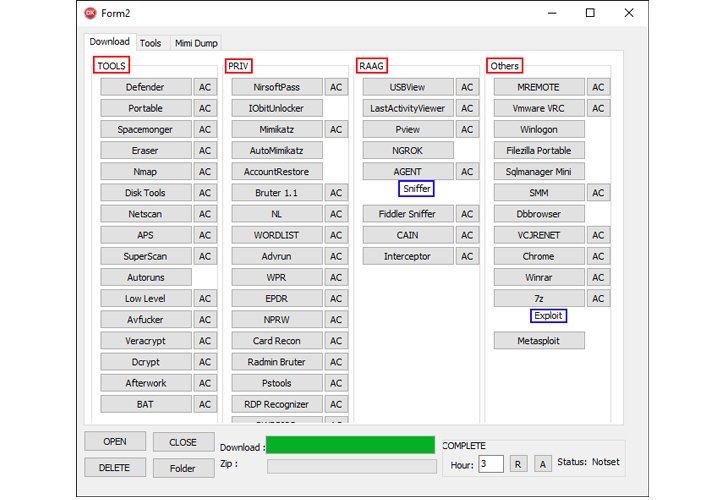
The primary component of Spacecolon is ScHackTool, a Delhi-based orchestrator that’s used to deploy an installer, which, as the name implies, installs ScService, a backdoor with features to execute custom commands, download and execute payloads, and retrieve system information from compromised machines.
ScHackTool also functions as a conduit to set up a wide array of third-party tools fetched from a remote server (193.149.185[.]23). The ultimate goal of the attacks is to leverage the access afforded by ScService to deliver a variant of the Scarab ransomware.

An alternate version of the infection chain identified by ESET entails the use of Impacket to deploy ScService as opposed to using ScHackTool, indicating that the threat actors are experimenting with different methods.
CosmicBeetle’s financial motives are further bolstered by the fact that the ransomware payload also drops a clipper malware to keep tabs on the system clipboard and modify cryptocurrency wallet addresses to those under the attacker’s control.
Furthermore, there is evidence that the adversary is actively developing a new ransomware strain dubbed ScRansom, which attempts to encrypt all hard, removable, and remote drives using the AES-128 algorithm with a key generated from a hard-coded string.
“CosmicBeetle doesn’t make much effort to hide its malware and leaves plenty of artifacts on compromised systems,” Souček said. “Little to no anti-analysis or anti-emulation techniques are implemented. ScHackTool relies heavily on its GUI, but, at the same time, contains several nonfunctional buttons.”
“CosmicBeetle operators use ScHackTool mainly to download additional tools of choice to compromised machines and run them as they see fit.”
[ad_2]
Source link