[ad_1]
Thousands of Citrix Application Delivery Controller (ADC) and Gateway endpoints remain vulnerable to two critical security flaws disclosed by the company over the last few months.
The issues in question are CVE-2022-27510 and CVE-2022-27518 (CVSS scores: 9.8), which were addressed by the virtualization services provider on November 8 and December 13, 2022, respectively.
While CVE-2022-27510 relates to an authentication bypass that could be exploited to gain unauthorized access to Gateway user capabilities, CVE-2022-27518 concerns a remote code execution bug that could enable the takeover of affected systems.
Citrix and the U.S. National Security Agency (NSA), earlier this month, warned that CVE-2022-27518 is being actively exploited in the wild by threat actors, including the China-linked APT5 state-sponsored group.
Now, according to a new analysis from NCC Group’s Fox-IT research team, thousands of internet-facing Citrix servers are still unpatched, making them an attractive target for hacking crews.
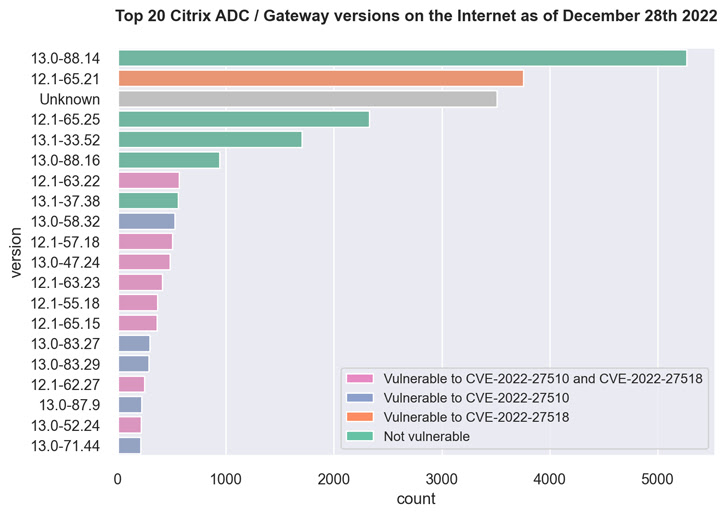
This includes over 3,500 Citrix ADC and Gateway servers running version 12.1-65.21 that are susceptible to CVE-2022-27518, as well as more than 500 servers running 12.1-63.22 that are vulnerable to both flaws.
A majority of the servers, amounting to no less than 5,000, are running 13.0-88.14, a version that’s immune to CVE-2022-27510 and CVE-2022-27518.
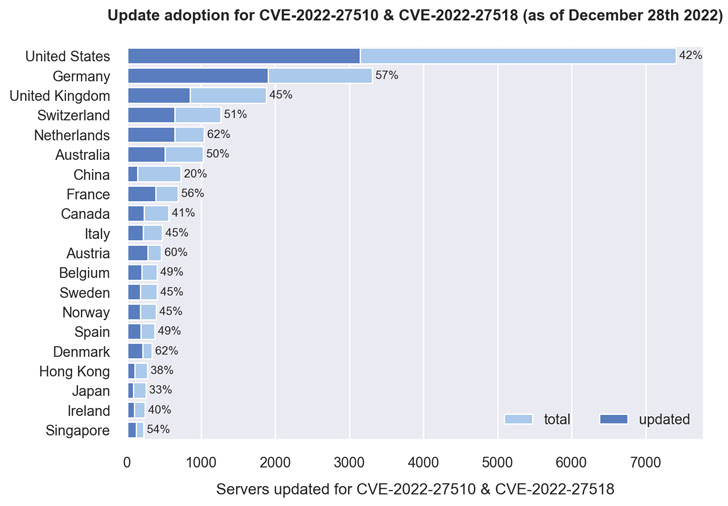
A country-wise breakdown shows that more than 40% of servers located in Denmark, the Netherlands, Austria, Germany, France, Singapore, Australia, the U.K., and the U.S. have been updated, with China faring the worst, where only 20% of nearly 550 servers have been patched.
Fox-IT said it was able to deduce the version information from an MD5-like hash value present in the HTTP response of the login URL (i.e., “ns_gui/vpn/index.html”) and mapping it to their respective versions.
[ad_2]
Source link